SDK Authentication & SSO
Authentication & SSO using SIMS ID and OAuth2.0
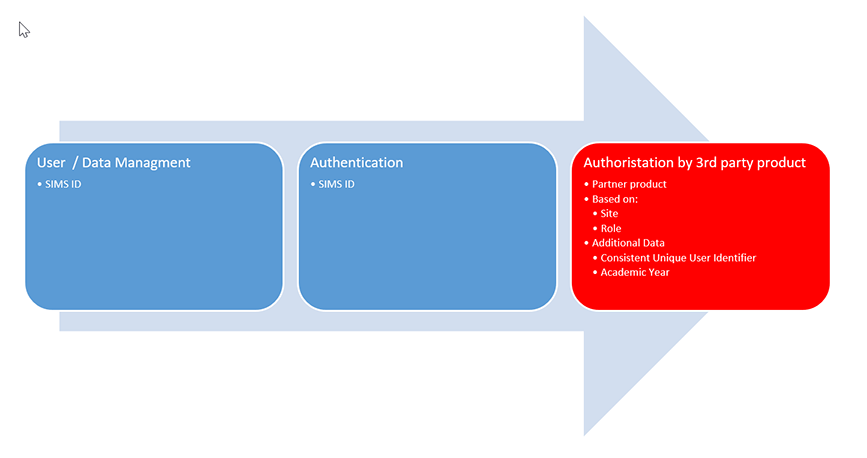
SIMS ID can provide federated authentication services to your product providing a single sign-on (SSO) experience to joint customers, allowing them to use their familiar username and password to access your product. This removes barriers to access, and lessens the administration overhead associated with the adoption of a new service with its accompanying usernames and passwords.
This authentication can assert a number of attributes for the user, ranging from simply the site(s) they are associated with through to more complex person and relationship data.
Using OAUTH 2.0 and SAML 2.0 authentication integration is achieved using recognised standards and protocols
Sample Clients and Settings for OAUTH 2.0
Sample clients are available to aid in developing against the SIMS OPEN ID Connection Specification. The ZIP file below contains a sample client. Client configuration details that will need to be included in the configuration of the sample client app are available on request.
This is a sample Hybrid C# MVC Web Application that will need to be populated with specific test client details that will be provided for your organisation in the SIMS ID live environment. The SI . Where you are also a SIMS Partner, the organisation will be common to any developments you are doing against SIMS Primary APIs.
Download a sample client application
Useful information
The web.config details of the client will need to be filled in with your ClientId, scopes and our URI settings. You will need set your secret value. All of these settings will be provided following the return of the SIMS ID Partner agreement.
The application is required to be run on https://localhost:5454. You will need to provide your hosting details so that the appropriate redirecturi settings for your client can be populated along with post logout redirect uri values. You will also need a test SSL certificate, however, this can simply be a self-signed certificate installed for the application.
The sample app has a page “../Debug/Tokens” where you can see the Access and Identity tokens, this will assist you in your integration.
Useful Details for SSO integration:
Our OpenId .well-known endpoint can be found here: https://sts.sims.co.uk/.well-known/openid-configuration
STS Base URI: https://sts.sims.co.uk
Logout Endpoint =
{STSBase}/connect/endsessionToken Endpoint =
{STSBase}/connect/tokenUser Info Endpoint =
{STSBase}/connect/userinfoIdentity Token Validation Endpoint =
{STSBase}/connect/identitytokenvalidationToken Revocation Endpoint =
{STSBase}/connect/revocationSettings (core ones of interest):
Consent Required : currently to off, this will be turned on for your Live client
Allow Remember Consent: allows the above to be persisted for the user
Logout Session Required: on logging out it will end the sessions
Require Sign Out Prompt: when logging out you get a prompt screen asking to confirm you want to log out, before actually logging out
Scopes:
openid
profile
roles
partner
All of the above are configurable and we can adjust to your needs, however the above is the most restrictive settings.
SIMS ID is based on IdentityServer3, and there is a large amount of resources available online. A good starting point is https://identityserver.github.io/Documentation/docsv2/resources/home.html
The following is bespoke to your implementation and will be provided by secure means:
Client Id
Client Name
Client Secret
This client is linked to your SIMS Primary organisation in the Live system you will have 2 users for:
Admin User: to be sent separately by secure mail
Staff User : to be sent separately by secure mail
The admin user can create user(s) in the site using the normal SIMS ID functionality, guide is available from the menu under the Users name.
SAML for SSO interactions
SAML integration outside of OAUTH 2.0 is not a preferred methodology, and we favour the OAUTH 2.0 approach. However, we can, and do, handle other SAML 2.0 interactions where necessary. Please contact to discuss your requirements.
Shibboleth for SSO interactions
Shibboleth can be supported.
UKAMF for SSO interaction
SIMS ID is registered with UKAMF.
Shibboleth 2.0 endpoint that supports WAYFless
You can review our endpoint attributes by using the UK Federation Test Service Provider at https://test.ukfederation.org.uk/ and specifically, the test Service provided for the UK Federation Central Discovery Service
A WAYFless URL can also be generated using the UK Federation WU-GEN service
The metadata provided by the SIMS ID Shibboleth endpoint can be seen at Live https://sso.sims.co.uk/metadata Staging [https://r4csso.identityfor.co.uk/metadata]